Milestone #3 Ethical Hacking Section W01 Fall Semester 2023 CO
Given an unencrypted AES key and an encrypted message, (attached) build a solution to decrypt the encrypted message and display its contents. The dataset for this milestone is attached to this dropbox
Hint: You may want to do some research into AES. Is the key the only thing you need?
Deliverables:
1. The name of the file matching the hash
2. Any source code (commented and readable) involved.
- If you used a pre-existing tool or tools, instead of source code, a list of the tools and a description of how you used them to identify the correct file.
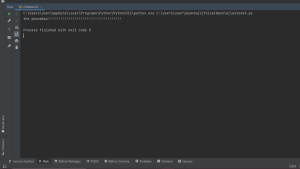
This problem has been solved
Milestone #3 Ethical Hacking
